Does our approach to data security meet your business needs?
Create a free business account today
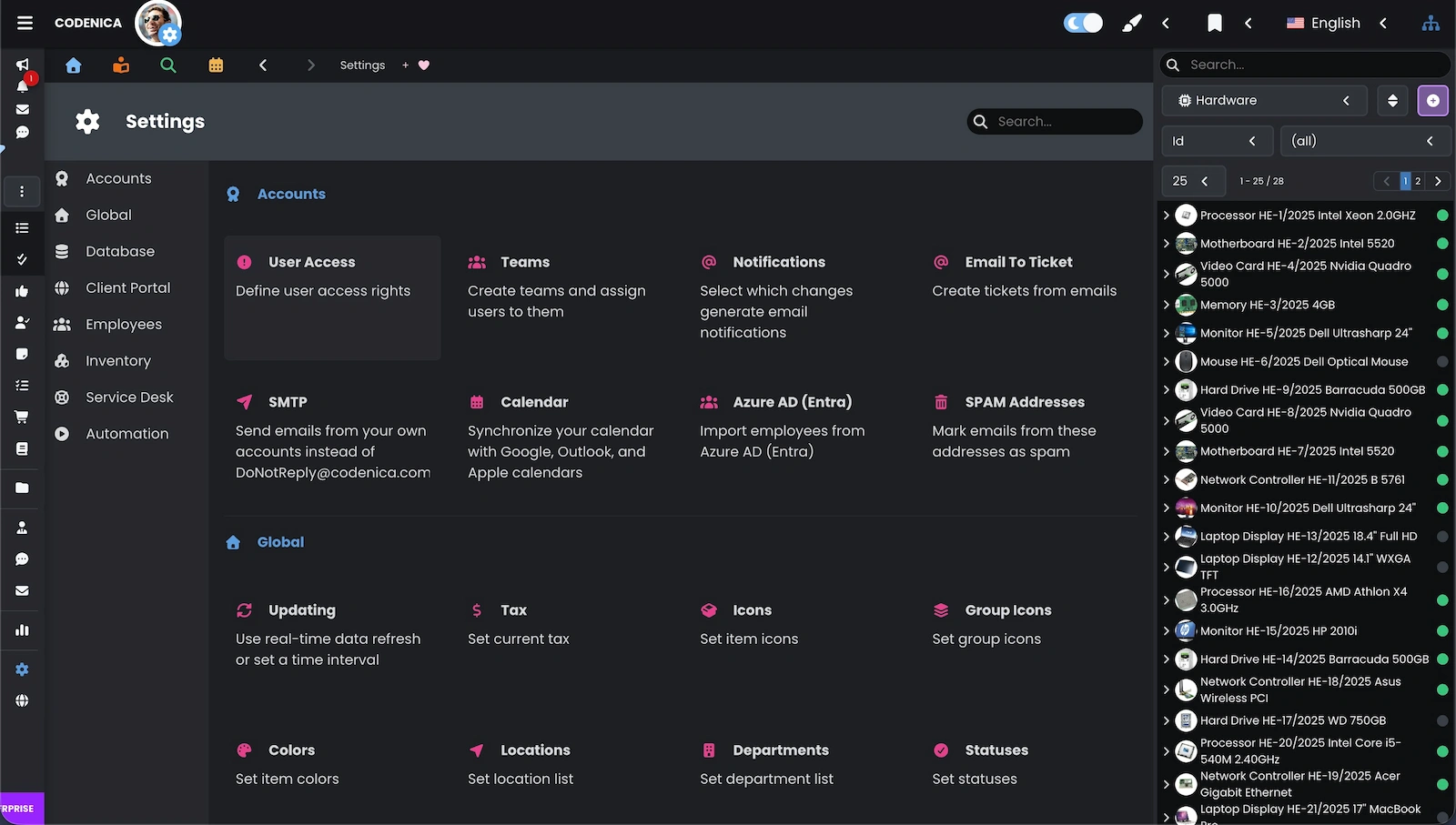
Codenica ITSM + ITAM runs on Microsoft Azure and uses encryption, isolated storage, and role-based access control to protect IT asset management and help desk operations. This ensures secure data processing and stable system performance.
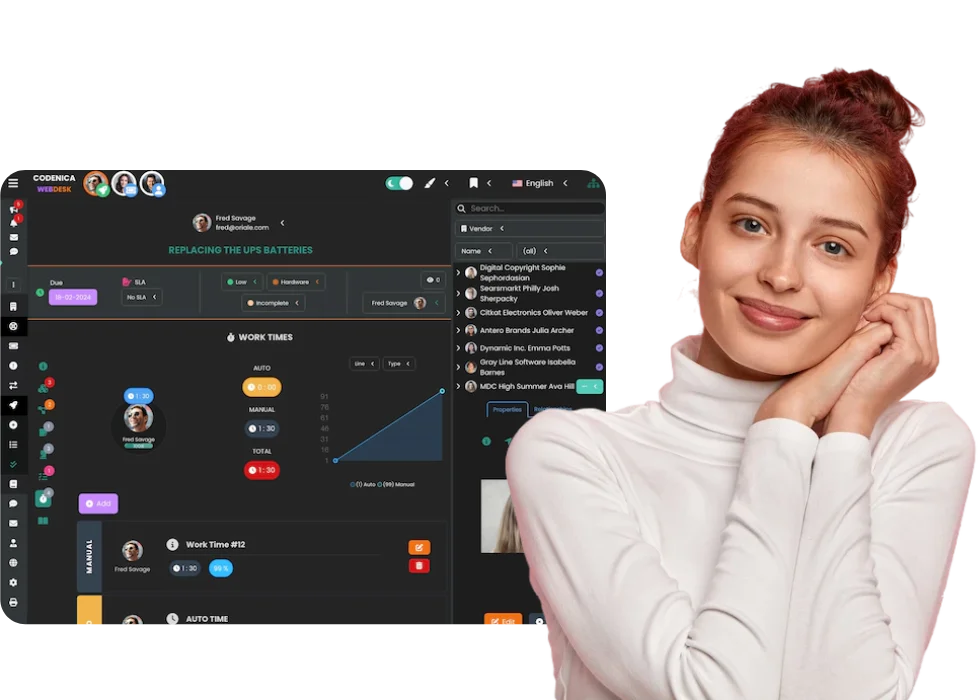
Codenica ITSM + ITAM is built entirely on Microsoft Azure, supporting secure data processing, stable performance, and compliance for organizations working with sensitive information.
Data in Codenica ITSM + ITAM is protected during transmission, storage, and user access. We use Microsoft Azure encryption and isolation mechanisms to protect company information and control who can access it.
Data Protection in Transit (HTTPS)
All communication between the user’s browser and the Codenica ITSM + ITAM system is performed exclusively over encrypted HTTPS connections. This protects data transmitted during system usage - including ticket content, user information, and attachments - against interception or modification during transmission.
Private Repositories in Azure
System data is stored in private repositories operating within isolated Microsoft Azure subnets. These repositories are not publicly accessible from the internet, and access is strictly controlled through network-level restrictions and application permissions. This approach significantly reduces the attack surface and protects data from unauthorized external access.
Secure File Storage and Authorized Access
Attachments, images, and documents stored in Codenica ITSM + ITAM are saved in secure repositories that can only be accessed through authorized, time-limited access mechanisms. Files are not publicly exposed, and viewing is restricted exclusively to users with appropriate permissions defined within the system.
Access control is a fundamental element of IT environment security. Codenica ITSM + ITAM enables precise definition of user permissions so that each user has access only to the functions and data required for their role within the organization.
Data Security as a System Foundation
In Codenica ITSM + ITAM, data security is built into the system architecture. The platform runs on Microsoft Azure and uses proven mechanisms for data protection, environment isolation, and access control. This protects data during storage, processing, and user access, while supporting stable and compliant daily operation.
The security of Codenica ITSM + ITAM is not based solely on Microsoft Azure cloud infrastructure, but also on continuous operational processes that minimize risk and ensure service continuity. The mechanisms below complement the system architecture and are responsible for its day-to-day resilience against threats.
Does our approach to data security meet your business needs?
Create a free business account today